System auditing is a comprehensive process that monitors and records activities across a Linux system to ensure security, compliance, and operational integrity. It involves monitoring file integrity, analyzing access logs, auditing sudo commands, tracking system events, and verifying compliance with organizational policies and regulations.
Through auditing, administrators can detect unauthorized changes, suspicious behaviors, and security breaches in real-time or via periodic audit log review.
File Integrity Monitoring
File Integrity Monitoring (FIM) is a security practice that tracks unauthorized or unexpected changes to critical system files and directories, helping administrators detect potential security breaches or misconfigurations. It works by monitoring modifications such as file writes, permission or attribute changes, and access events that could indicate malicious activity or policy violations.
Common tools used for file integrity monitoring include auditd, the Linux Audit system that records detailed system events based on defined rules, and dedicated file integrity checkers such as AIDE or Tripwire, which compare current file states against a known secure baseline.
Audit rules are configured to specify which files or directories should be watched and what types of actions—such as write operations, attribute changes, or access attempts—should trigger logging and alerts.
Example auditd rule to monitor /etc/passwd:
auditctl -w /etc/passwd -p wa -k passwd_changes-w: watch file
-p wa: watch write and attribute changes
-k: key to filter logs easily
Access Logs Analysis
System authentication and security logs such as /var/log/auth.log, /var/log/secure, and sudo logs capture detailed information about authentication attempts, user login activities, and privilege escalation events.
These logs record both successful and failed login attempts, as well as commands executed with elevated privileges, providing valuable insight into user behavior and system access patterns.
Regularly monitoring these logs helps administrators identify failed or suspicious login attempts, detect unauthorized access, and track command execution history, which is essential for auditing, troubleshooting, and strengthening overall system security.
Example check for sudo command usage:
grep "COMMAND=" /var/log/auth.logsudo Audit Logs
Sudo audit logs record all sudo command executions along with timestamps and detailed user information, providing a clear record of who performed privileged actions on the system and when.
Proper configuration in /etc/sudoers or through audit rules applied to sudo-related logs ensures that these events are consistently captured and stored for review.
By maintaining comprehensive sudo audit logs, organizations enable strong accountability, support compliance requirements, and facilitate forensic analysis of privilege escalations during security investigations.
System Event Auditing
The Linux Audit Framework (auditd) records system calls, user activities, and security-related events. Logs include detailed event types, timestamps, user IDs, and process information. Commands like ausearch and aureport facilitate searching and reporting of audit logs.
Example: Search for file permission changes:
ausearch -k file_modifications -i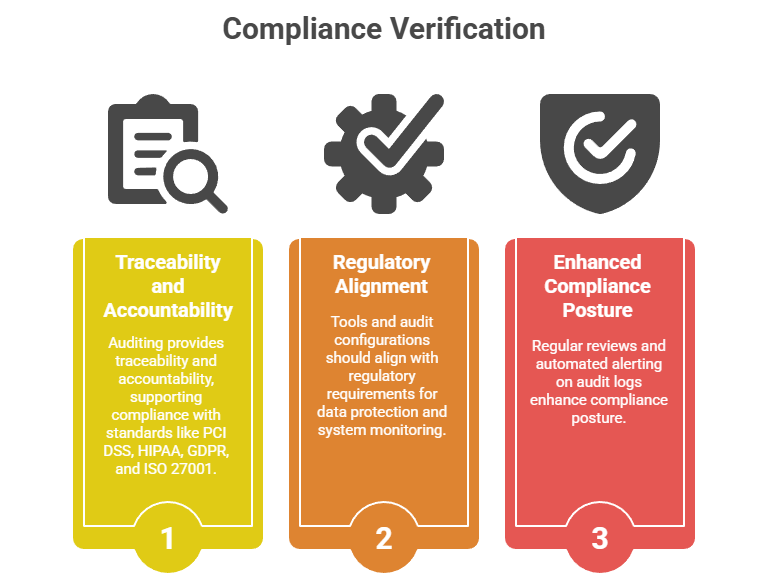
Class Sessions
Sales Campaign

We have a sales campaign on our promoted courses and products. You can purchase 1 products at a discounted price up to 15% discount.