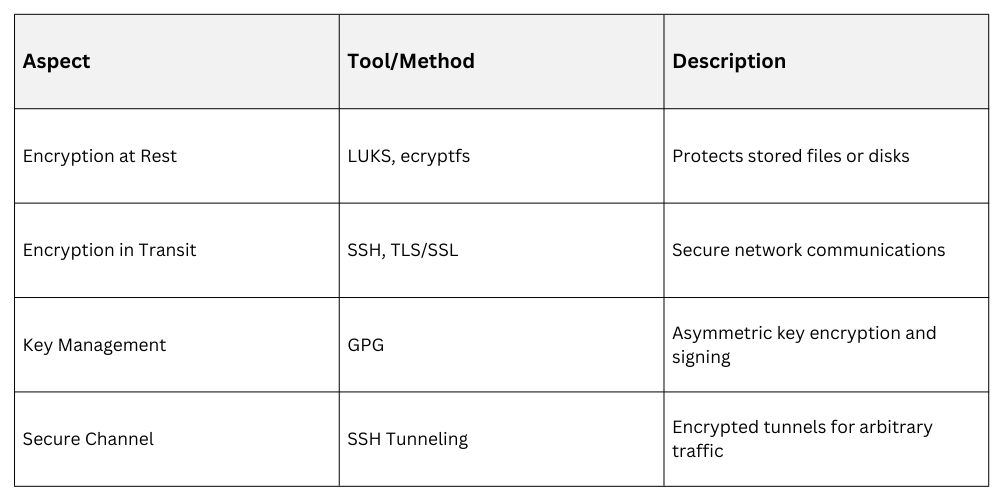
Encryption and secure communication protocols are essential for protecting data confidentiality, integrity, and authenticity in Linux systems. These mechanisms ensure that sensitive information remains inaccessible to unauthorized parties both at rest and in transit.
Tools like GPG enable cryptographic key management and data signing, SSH tunneling provides secure encrypted channels, while TLS/SSL certificates protect web and application traffic. Additionally, encrypted file storage and data protection during transfer are critical components of a secure Linux environment.
GPG and Cryptographic Key Management
GPG (Gnu Privacy Guard) implements the OpenPGP standard for encryption and signing of data and emails. Users generate key pairs: private (kept secret) and public (shared).
Commands:
1. Generate key:
gpg --full-generate-key2. Encrypt file with recipient’s public key:
gpg --encrypt --recipient user@example.com file.txt3. Decrypt file with private key:
gpg --decrypt file.txt.gpgSign and verify signatures for integrity and authenticity.
SSH Tunneling
SSH tunnels encapsulate network traffic inside an encrypted SSH connection, protecting data transfer from eavesdropping. It supports local, remote, and dynamic (SOCKS) port forwarding.
Example local port forwarding:
ssh -L 8080:internalhost:80 user@sshserverSecures legacy applications that lack native encryption.
TLS/SSL Certificates
TLS (Transport Layer Security) and SSL (Secure Sockets Layer) provide encrypted communication channels over TCP/IP, commonly used to secure HTTPS connections and APIs. Certificates issued by trusted Certificate Authorities (CAs) verify the identity of servers, ensuring secure interactions.
Tools such as openssl are used to generate and manage private keys and certificates, while mutual TLS (mTLS) extends this security by authenticating both the server and the client.
Encrypted File Storage
Linux supports file encryption via tools like ecryptfs, LUKS/dm-crypt for full disk encryption, ensuring data protection at rest. File-level encryption tools integrate with access controls and key management for secure storage.
Data Encryption at Rest and in Transit