Data privacy and security are critical pillars of modern healthcare because patient information is among the most sensitive forms of data.
Healthcare organizations collect vast amounts of personal, medical, genetic, and behavioral information, which must be protected against unauthorized access, misuse, or cyber threats.
With the rapid digitization of healthcare through EHRs, telemedicine, mobile health applications, and wearable devicesthe risk of data breaches and identity theft has grown significantly.
Ensuring privacy means giving patients control over their information, maintaining confidentiality, and complying with legal and ethical guidelines.
Security, on the other hand, focuses on protecting systems and data from unauthorized access through technical safeguards such as encryption, authentication, access control, and continuous monitoring.
Regulations like HIPAA (U.S.), GDPR (Europe), and India’s emerging Digital Personal Data Protection Act (DPDPA) define how healthcare data should be stored, shared, and protected.
Healthcare providers must also consider secure cloud storage, safe API integrations, and strong cybersecurity defenses to prevent attacks such as ransomware, phishing, or data leaks.
As healthcare becomes increasingly interconnected, maintaining robust privacy and security practices is essential for building trust, ensuring patient safety, and enabling safe data sharing for analytics, research, and AI applications.
Effective privacy and security frameworks also support scalable digital health ecosystems by minimizing risks while promoting innovation.
Data Protection and Security in Digital Healthcare
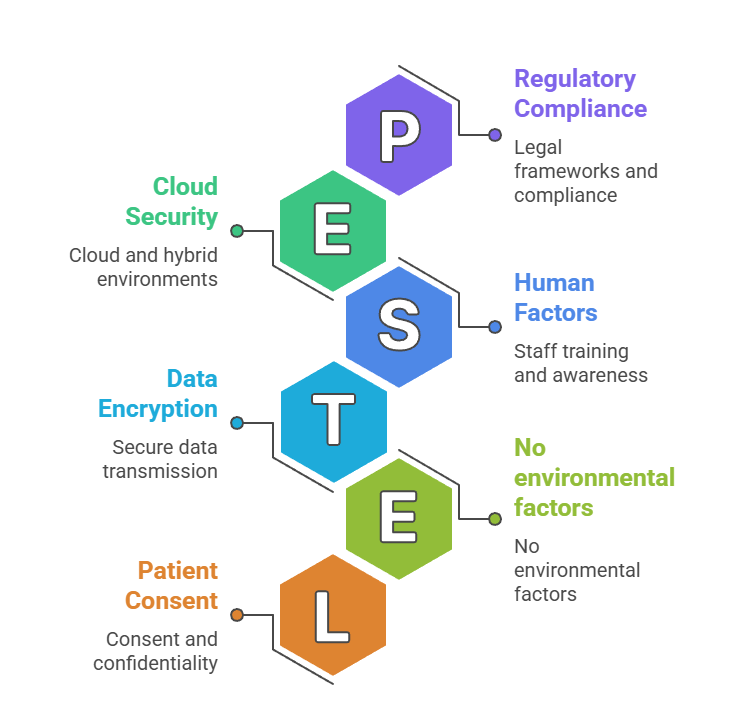
1. Importance of Patient Consent and Confidentiality
Patient consent is the foundation of healthcare privacy, ensuring that individuals understand how their data will be used, shared, or stored.
Confidentiality builds trust, encouraging patients to share accurate information required for appropriate diagnosis and care.
Modern healthcare systems include consent management tools allowing patients to approve or restrict data sharing across providers and digital platforms.
Consent also becomes essential when using data for AI training, research studies, or cross-institution analytics. Clear consent workflows help organizations comply with international privacy regulations and reduce legal risks.
By empowering patients to make informed decisions, consent and confidentiality frameworks enhance ethical data practices and strengthen patient engagement in their own care.
2. Encryption and Secure Data Transmission
Encryption ensures that healthcare data remains unreadable to unauthorized parties during storage or transmission. Both at-rest and in-transit encryption protect information sent between hospital systems, cloud servers, telemedicine platforms, and connected medical devices.
Secure communication protocols like HTTPS, SSL/TLS, and VPNs safeguard data exchanged across networks. Encryption also helps prevent interception during cyberattacks such as man-in-the-middle attacks or data sniffing.
Modern systems use end-to-end encryption to protect patient information from the point of collection to final storage. As healthcare becomes more mobile and cloud-based, strong encryption standards are crucial for maintaining confidentiality and preventing data leaks.
3. Access Control and Authentication Mechanisms
Access control ensures that only authorized healthcare staff can view, modify, or share patient data based on their roles and responsibilities.
Role-Based Access Control (RBAC), biometric authentication, multi-factor authentication (MFA), and password policies help protect systems from internal misuse or external breaches.
Limiting access prevents accidental or intentional exposure of sensitive information.
Audit trails and activity logs allow organizations to track who accessed data and when, supporting compliance with regulatory requirements. Proper authentication mechanisms also reduce insider threats, one of the most common causes of healthcare data breaches.
Robust access control systems maintain data integrity and enhance accountability across healthcare workflows.
4. Securing Networks, Devices, and IT Infrastructure
Healthcare organizations must secure not only databases but also networks, endpoints, connected devices, and server environments.
Network firewalls, intrusion detection systems (IDS), antivirus tools, and regular vulnerability assessments protect against cyber threats.
As hospitals increasingly adopt IoT devices like pacemakers, insulin pumps, and wearable sensors, securing medical devices becomes critical to preventing hacking or manipulation.
Cloud environments require additional layers of protection, including data segregation, access policies, and real-time monitoring.
Regular patching and updates reduce vulnerabilities that attackers could exploit.
A secure infrastructure minimizes the risk of downtime, data corruption, or unauthorized access, ensuring continuous and safe healthcare delivery.
5. Regulatory Compliance and Legal Frameworks
Healthcare organizations must comply with strict privacy laws that govern how patient data is collected, stored, processed, and shared.
Regulations like HIPAA, GDPR, and India’s Digital Personal Data Protection Act (2023) mandate data minimization, breach reporting, consent collection, and strong security practices.
These laws impose financial penalties for non-compliance, encouraging organizations to adopt better governance and auditing practices.
Compliance frameworks ensure transparency in handling patient information and set standards for cross-border data sharing.
They also guide how long data must be retained and when it must be deleted.
Adhering to regulatory requirements protects patients’ rights and ensures ethical data usage across the healthcare ecosystem.
6. Audit Trails, Monitoring, and Incident Response
Audit trails play a critical role in healthcare security by recording every access, modification, or transfer of patient data within a system. These logs help organizations detect unusual activity, identify unauthorized access, and trace the source of security issues.
Continuous monitoring tools analyze network behavior in real time, allowing early detection of threats such as ransomware or system intrusion.
A well-defined incident response plan ensures that, in case of a breach, the organization can take immediate actions such as isolating affected systems, notifying stakeholders, and preventing further damage.
These practices minimize downtime and reduce the impact of cyberattacks. By combining monitoring, auditing, and rapid response systems, healthcare organizations enhance accountability and protect patient safety.
7. Data Anonymization and De-identification
Anonymization removes personally identifiable information from datasets to ensure that individuals cannot be traced, even when data is used for research, AI training, or large-scale analytics.
Techniques like masking, pseudonymization, aggregation, and differential privacy preserve data utility while protecting identity.
These processes are essential for complying with privacy laws, especially when sharing data across organizations or using it for public health studies.
De-identified data enables innovation by allowing AI models to train on large datasets without compromising patient privacy.
However, healthcare systems must implement strong safeguards to prevent re-identification attacks, particularly when datasets are combined.
Anonymization is therefore a core component of ethical and secure data science in healthcare.
8. Risk Assessment and Vulnerability Management
Regular risk assessments help healthcare organizations identify weaknesses in their digital infrastructure, security processes, and data handling workflows.
These assessments evaluate potential threats including system flaws, outdated software, human errors, and device vulnerabilities—and prioritize actions to mitigate them.
Vulnerability management involves patching security gaps, updating software, monitoring device integrity, and continuously improving defensive measures.
It also includes penetration testing to simulate cyberattacks and evaluate system resilience. By conducting ongoing risk assessments, healthcare institutions reduce exposure to breaches and ensure compliance with regulatory standards.
This proactive approach helps safeguard both patient information and organizational reputation.
9. Security in Cloud and Hybrid Healthcare Environments
With the rapid adoption of cloud-based EHRs, telehealth platforms, and remote monitoring systems, securing cloud environments has become essential.
Cloud security includes data encryption, identity management, secure APIs, firewalls, and compliance-approved hosting environments.
Hybrid infrastructures where on-premise systems integrate with cloud platforms require additional layers of protection such as secure tunnels, role-based access, and network segmentation.
Cloud providers often follow strict international standards (ISO/IEC 27001, HITRUST), offering robust protections, but healthcare organizations must still configure and manage their security responsibly.
Ensuring secure cloud workflows allows healthcare systems to scale analytics, store massive datasets, and maintain service continuity without compromising patient privacy.
10. Human Factors and Staff Training in Security
Human error remains one of the leading causes of data breaches in healthcare, making staff training an essential component of security.
Employees must be trained to recognize phishing emails, avoid sharing passwords, follow proper documentation practices, and securely handle devices or patient records.
Awareness programs also help staff understand the importance of compliance with privacy regulations, secure communication protocols, and safe use of digital tools.
Regular simulations and refresher training ensure that staff stay updated on emerging threats.
When healthcare workers understand the risks and follow established guidelines, organizations significantly reduce the possibility of accidental data exposure or internal misuse.
