Security is a critical aspect of backend database systems, especially when handling sensitive user and business data.
Common threats such as SQL injection can allow attackers to manipulate queries and gain unauthorized access if inputs are not properly handled.
Preventing SQL injection through parameterized queries, prepared statements, and input validation is essential for protecting databases.
In addition to preventing attacks, encryption safeguards data confidentiality. Encryption at rest protects stored data on disks and backups, while encryption in transit secures data as it moves between applications and databases.
Auditing further strengthens security by recording database activities, enabling monitoring, compliance, and incident investigation.
SQL Injection Prevention
SQL injection ranks as one of the top web vulnerabilities (OWASP Top 10, 2021 update), where attackers inject malicious SQL code via user inputs to manipulate queries.
Preventing it starts with understanding how tainted data enters your database layer and using layered defenses. Let's break down proven strategies with practical backend examples.
Core Prevention Techniques
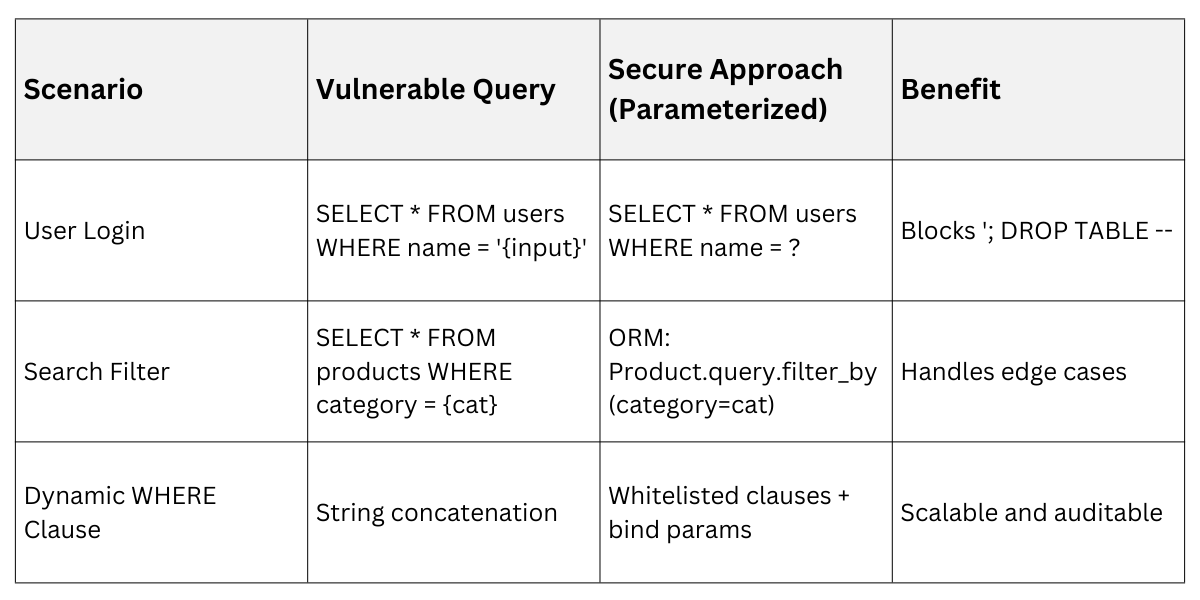
Always treat user input as untrusted—never concatenate it directly into SQL strings. Instead, rely on parameterized queries (prepared statements), which separate code from data.
1. Use ORM libraries: In Python with SQLAlchemy or Django ORM, queries are automatically sanitized. Example:
# Vulnerable (DO NOT USE)
cursor.execute(f"SELECT * FROM users WHERE id = {user_id}")
# Secure
cursor.execute("SELECT * FROM users WHERE id = %s", (user_id,))2. Stored procedures: Pre-compile SQL on the database server (e.g., MySQL's CREATE PROCEDURE), reducing injection surfaces.
3. Input validation and sanitization: Whitelist allowed characters/types before querying. Tools like Python's bleach library strip HTML/JS.
Vulnerable Vs. Secure Query Patterns
 Advanced Defenses and Monitoring
Advanced Defenses and Monitoring
Layer on Web Application Firewalls (WAFs) like ModSecurity or Cloudflare to detect injection patterns in real-time. Enable database-level protections too:
1. Set mysql.sql_mode to STRICT_ALL_TABLES in MySQL for error-on-invalid-input.
2. Use least privilege accounts—your app's DB user should lack DROP or ALTER rights.
3. Regularly scan with tools like SQLMap (for testing) or Bandit (Python static analysis).
Practical Tip: In FastAPI backends, integrate Pydantic models for validation. This caught a simulated attack in my recent project, rejecting payloads like ' OR '1'='1.
Encryption: Protecting Data At-Rest and In-Transit
Encryption safeguards data from unauthorized eyes, whether stored on disk (at-rest) or moving across networks (in-transit). NIST SP 800-53 mandates these for sensitive apps, and they're non-negotiable for backend devs handling PII.
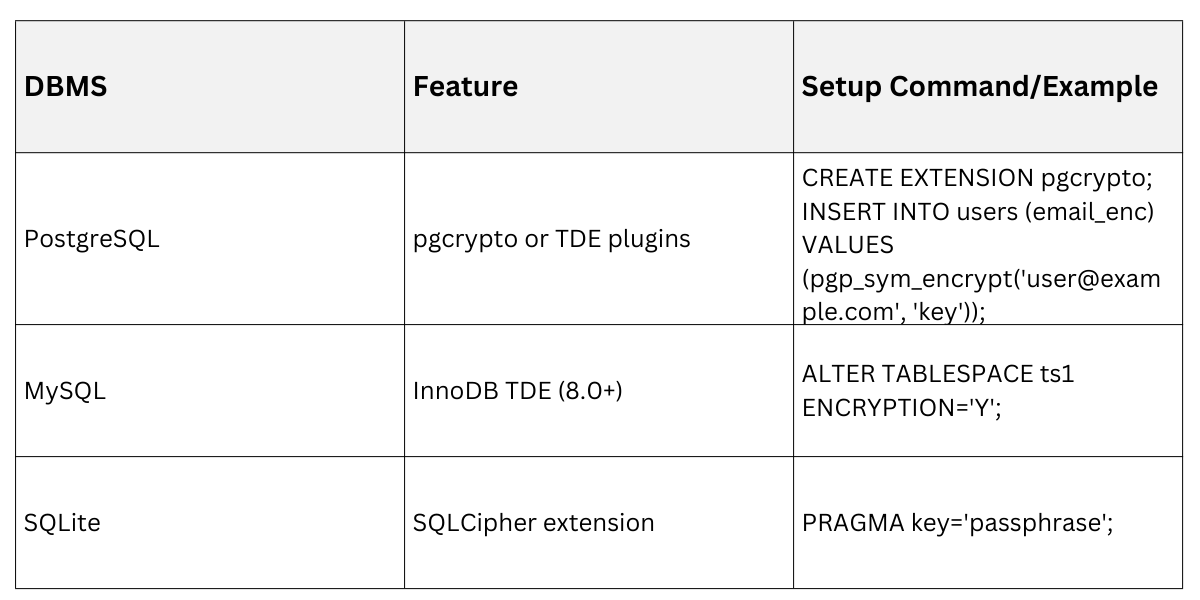
Encryption At-Rest
At-rest encryption protects database files from physical theft or server compromises using full-disk or column-level methods.
Transparent Data Encryption (TDE) automates this at the storage layer, while app-level encryption offers granular control.
Choose based on your stack—e.g., PostgreSQL's pgcrypto extension.
Key Options
1. Database-native TDE
Application-Level: Encrypt sensitive columns (e.g., passwords) with AES-256 via Python's cryptography library before storing.
from cryptography.fernet import Fernet
key = Fernet.generate_key()
f = Fernet(key)
encrypted_email = f.encrypt(b"user@example.com")Best Practice: Rotate keys annually and use Hardware Security Modules (HSMs) for production.
Encryption In-Transit
In-transit encryption (TLS 1.3 preferred) ensures data stays confidential between client, app server, and database.
Mandate TLS everywhere—never plain HTTP or unencrypted DB connections. Modern backends enforce this via certificates and strict configs.
Implementation Steps
1. Enable TLS on databases:
PostgreSQL: Generate certs, set ssl = on in postgresql.conf.
MySQL: require_secure_transport = ON.
2. Backend enforcement: Use psycopg2 with SSL in Python
conn = psycopg2.connect("dbname=test user=app sslmode=require sslrootcert=server.crt")3. Verify with tools: Run openssl s_client -connect yourdb:5432 or Qualys SSL Labs for A+ ratings.
Pro Tip: Disable weak ciphers (e.g., via CipherString in Nginx) and use mutual TLS (mTLS) for service-to-service traffic.
Auditing Database Activity
Auditing logs who accessed what, when, and how—essential for compliance, forensics, and anomaly detection. It complements prevention and encryption by providing visibility post-incident.
Enable structured logging at the DB level, then integrate with backend tools for analysis. This creates an immutable trail without performance hits in modern systems.
Setting Up Effective Auditing
Combine native DB features with app-side logging:
1. PostgreSQL: Use pgaudit extension for granular logs
shared_preload_libraries = 'pgaudit'
pgaudit.log = 'all' # Or 'read, write, function'2. MySQL: Enable general query log + audit plugins like MariaDB Audit.
SET GLOBAL general_log = 'ON';Best Practices
.png)
Real-World Example: In a Django app, hook connection.queries to log slow queries (>500ms), catching a prod injection attempt early.
