Data security in Business Intelligence (BI) environments is crucial to protect sensitive business information from unauthorized access, breaches, and misuse. As BI systems aggregate, analyze, and visualize data from various sources, they become attractive targets for cyber threats.
Ensuring robust data security within BI entails applying multi-layered strategies that safeguard data confidentiality, integrity, and availability while enabling authorized users to derive value.
Identity and Access Management (IAM)
Identity and access management are essential for protecting sensitive information and maintaining compliance. Here are recommended measures for robust access control.
1. Implement role-based access control (RBAC) to restrict data and resource access based on user roles and responsibilities.
2. Adopt multi-factor authentication (MFA) for all users accessing BI platforms to prevent unauthorized logins.
3. Use single sign-on (SSO) for consistent and secure user authentication across BI tools and related systems.
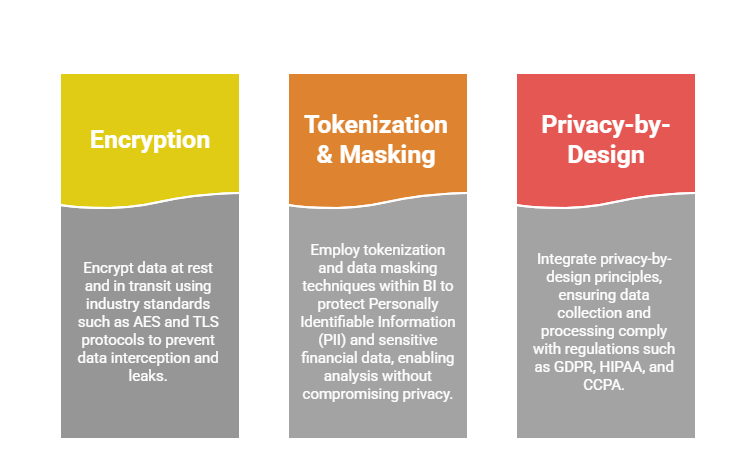
Data Encryption and Privacy
Maintaining data security and privacy is critical for trust and compliance. Below are key strategies for encryption, masking, and privacy-by-design.
Secure Data Connectivity
Protecting data in transit and managing access is essential for BI environments. Below are key strategies for secure connectivity and credential management.
1. Use data gateways or secure connectors to safely link on-premises data sources with cloud BI services, enforcing strong authentication and encrypted channels.
2. Prefer DirectQuery or Live Connection in BI tools for real-time data access while applying stringent security policies at the source.
3. Regularly review and restrict database credentials and permissions granted to BI tools to follow the least privilege principle.
Monitoring, Auditing, and Incident Response
Effective BI security requires continuous monitoring, auditing, and preparedness for incidents. Implement intrusion detection systems (IDS) and Security Information and Event Management (SIEM) solutions to track access patterns and detect suspicious activity.
Regular security audits and vulnerability assessments help identify and remediate weaknesses, while well-developed incident response plans ensure swift mitigation and compliance with notification requirements.
Governance and Compliance
Effective governance and compliance in BI involve creating a data governance framework with clear security policies, standards, and procedures throughout the data lifecycle.
Classifying data by sensitivity and applying appropriate labels ensures proper handling and controlled sharing within reports and dashboards. Additionally, training users on security best practices fosters awareness and reduces risks from insider threats and human error.
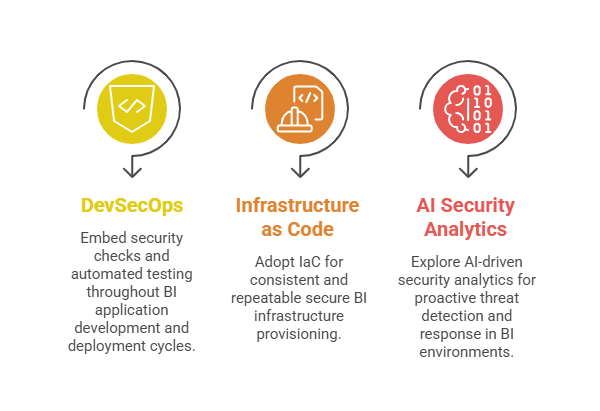
Emerging Security Technologies
Emerging security technologies are transforming how BI environments are protected, integrating automation, intelligence, and proactive measures. The following approaches illustrate key innovations in this space.