Implementing an Information Security Management System (ISMS) in real-world settings involves practical challenges, strategic planning, and continuous adaptation tailored to specific organizational contexts.
Real-world examples of ISMS implementation demonstrate how diverse organizations across industries have leveraged ISO/IEC 27001 standards to strengthen their information security posture, reduce risks, comply with regulations, and build trust with stakeholders.
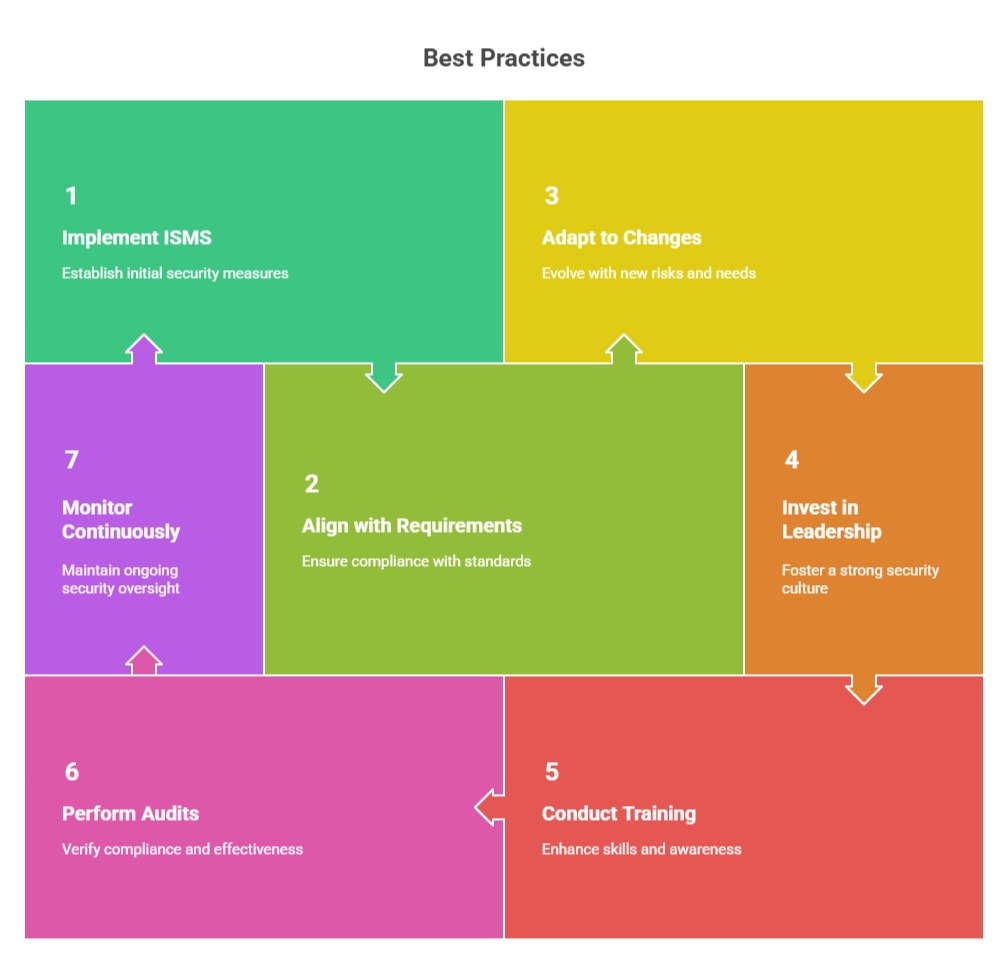
These cases highlight the benefits, lessons learned, and best practices that can guide others embarking on similar journeys.
Example Case Studies
1. Fintech Startup in Koramangala (Bangalore)
Challenge: Handling sensitive customer and transaction data without formal security controls, causing investor and client concerns.
Approach: Conducted risk assessments, documented controls, implemented access controls and encryption, and established incident response protocols with expert ISO 27001 consultancy.
Outcome: Achieved certification within six months, improving stakeholder trust, accelerating deal closures, and fostering a security-first culture.
2. SaaS HR Solutions Provider in HSR Layout (Bangalore)
Challenge: Inconsistent access management, a lack of security documentation, and insufficient data retention policies are troubling international clients in regulated sectors.
Approach: Centralized identity and access management, deployed cloud security policies aligned with ISO standards, and trained staff on secure development.
Outcome: Certification opened opportunities for new global contracts and reduced internal incidents by 40%, smoothing compliance audits.
3. IT Outsourcing Company in Whitefield (Bangalore)
Challenge: Security governance gaps, including user privilege issues and third-party access concerns, with client data protection on the line.
Approach: Developed internal security policies, business continuity plans, and vendor management audits, supported by regular internal audits.
Outcome: Enhanced operational maturity, decreased client churn, and secured larger multi-year contracts by meeting security benchmarks.
4. Financial Institution: Addressed cross-border regulatory compliance by implementing comprehensive risk management and audit frameworks, reducing audit findings by 30% and avoiding penalties. Demonstrated ISO 27001’s power to meet and exceed regulatory demands.
5. Healthcare Provider: Implemented stringent access controls and encryption to protect patient data, decreasing data breach risk by 40%. Enhanced staff security engagement through targeted training, illustrating ISO 27001’s effectiveness in sensitive data environments.
Class Sessions
Sales Campaign

We have a sales campaign on our promoted courses and products. You can purchase 1 products at a discounted price up to 15% discount.
