Operational processes for maintaining an Information Security Management System (ISMS) are essential to ensure it remains effective, compliant, and aligned with organizational objectives over time.
According to ISO/IEC 27001, the ISMS must be integrated into everyday business activities through ongoing planning, implementation, monitoring, and continual improvement.
Well-defined operational processes support consistent security performance, early detection of issues, and timely responses, enabling businesses to sustain their information security posture and certification status.
Key Operational Processes for ISMS Maintenance
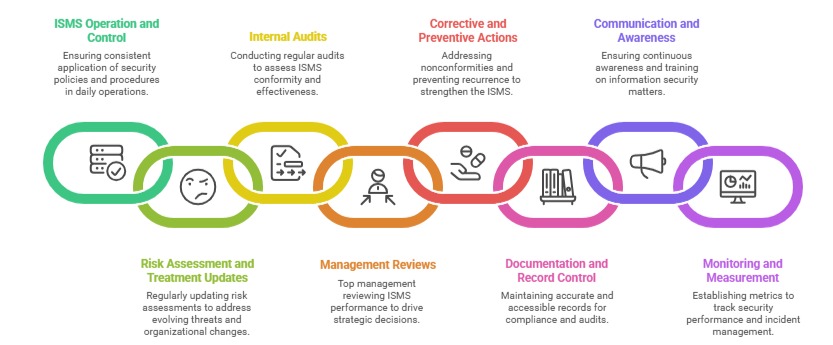
Continuous operation and improvement of an ISMS rely on several interconnected management processes. The list below highlights the key operational actions necessary for its ongoing effectiveness.
1. ISMS Operation and Control (Clause 8.1): Organizations must plan, implement, and control the processes needed to meet information security requirements. This includes ensuring that policies, procedures, and controls are applied consistently in daily operations.
Operational control also involves managing changes and documenting deviations, ensuring that security standards are upheld systematically.
2. Risk Assessment and Treatment Updates (Clause 8.2 & 8.3): Risk assessments and treatment plans must be periodically reviewed and updated to reflect evolving threats, organizational changes, or incidents. This keeps the ISMS current and responsive to new risks.
3. Internal Audits: Conducting regular internal audits assesses the conformity and effectiveness of the ISMS against ISO standards, policies, and legal requirements. Audits uncover gaps or nonconformities that require corrective actions, reinforcing continual improvement.
4. Management Reviews: Top management should review the ISMS performance regularly (typically biannually or annually) to evaluate audit results, risk management effectiveness, resource adequacy, stakeholder feedback, and improvement opportunities.
This process drives strategic decisions and supports leadership commitment.
5. Corrective and Preventive Actions: Organizations must have processes to address nonconformities by identifying root causes, taking corrective actions, and preventing recurrence. This cycle strengthens the ISMS and helps achieve compliance objectives sustainably.
6. Documentation and Record Control: Maintaining accurate, accessible, and up-to-date documented information is crucial for demonstrating regulatory compliance and facilitating audits. Document control processes include version management, review schedules, and secure storage.
7. Communication and Awareness: Operational processes should ensure continuous awareness, training, and effective communication related to information security matters among all employees and relevant external parties.
8. Monitoring and Measurement: Establishing metrics and monitoring mechanisms for key ISMS activities enables effective tracking of security performance. This includes monitoring security incidents, control effectiveness, and risk treatment progress.
Benefits of Effective Operational ISMS Processes
| Benefit | Description |
| Alignment with Business Goals | Ensures the ISMS remains continuously aligned with organizational objectives and evolving risks. |
| Early Issue Detection | Enables prompt identification and resolution of security issues before they escalate. |
| Regulatory and Certification Compliance | Supports adherence to legal, regulatory, and ISO certification requirements. |
| Proactive Management | Encourages ongoing monitoring, analysis, and improvement of information security processes. |
| Strong Security Culture | Fosters awareness, accountability, and continuous training among employees. |
| Evidence for Audits | Provides documented proof of due diligence and effective ISMS operation during audits. |
Class Sessions
Sales Campaign

We have a sales campaign on our promoted courses and products. You can purchase 1 products at a discounted price up to 15% discount.
