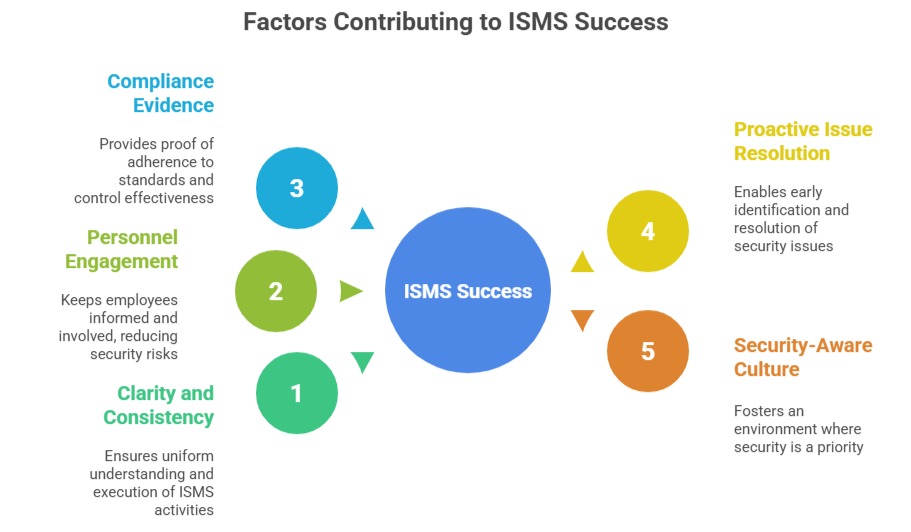
Documentation, communication, and awareness form foundational pillars in the effective operation and continual improvement of an Information Security Management System (ISMS) as prescribed by ISO/IEC 27001.
Clear and accurate documentation provides the formal recorded information needed to demonstrate compliance and guide consistent ISMS practices.
Equally important, effective communication ensures relevant information reaches appropriate stakeholders, fostering understanding and engagement.
Awareness programs promote security-conscious behavior among personnel, mitigating risks arising from human factors and strengthening the security culture.
Documentation Requirements
ISO 27001 mandates specific documentation termed "documented information," which includes policies, procedures, plans, reports, and records necessary for ISMS operation and auditability. Key mandatory documents and records include:
1. ISMS Scope (Clause 4.3)
2. Information Security Policy (Clause 5.2)
3. Risk Assessment and Treatment Methodologies and Reports (Clauses 6.1.2, 8.2)
4. Statement of Applicability (Clause 6.1.3)
5. Risk Treatment Plan (Clauses 6.1.3, 8.3)
6. Information Security Objectives (Clause 6.2)
7. Roles and Responsibilities definition (Clause 7.5)
8. Asset Inventory (Annex A.5.9)
9. Incident Response Procedures (Annex A.5.26)
10. Security Operating Procedures (Annex A.5.37)
11. Audit Plans and Reports (Clause 9.2)
12. Management Review Minutes (Clause 9.3)
13. Corrective Action Records (Clause 10.2)
Maintaining up-to-date and accessible documented information supports consistent ISMS implementation and demonstrates due diligence during certification or regulatory audits.
Communication in ISMS
Effective communication involves sharing relevant ISMS information internally and externally as appropriate. ISO 27001 Clause 7.4 requires organizations to establish processes for:
1. What information to communicate (policies, roles, responsibilities, security incidents)
2. To whom and when to communicate (staff, management, external partners)
3. How to communicate (meetings, emails, intranet, training sessions)
Open two-way communication enables prompt reporting of security incidents and feedback for improvement, ensuring alignment across all levels.
Security Awareness and Training
Human factors are often the weakest link in security. Clause 7.3 mandates organizations to ensure employees and relevant third parties are aware of their information security responsibilities and receive training suitable to their roles.
Awareness activities typically include:
1. Regular security awareness campaigns and newsletters
2. Role-specific training on policies, controls, and incident handling
3. Testing knowledge through quizzes or simulated phishing exercises
4. Inductions and refresher sessions to address evolving threats and controls
5. Strong awareness reduces risks related to human error, insider threats, and social engineering attacks.