Conducting risk assessments is a vital process within the ISO/IEC 27001 framework to systematically identify, analyze, and evaluate information security risks. This process helps organizations understand the likelihood and potential impact of threats exploiting vulnerabilities in their assets.
Evaluating risk impact enables informed decisions about which risks need treatment to protect information confidentiality, integrity, and availability. Effective risk assessment facilitates robust planning and resource allocation for an organization's Information Security Management System (ISMS).
Risk Assessment Methodology Steps
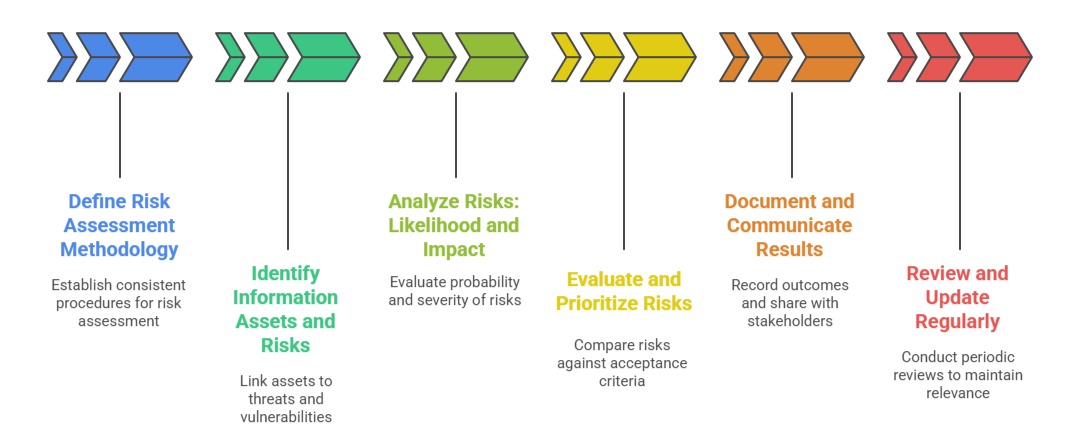
An organized methodology helps organizations measure, document, and address security risks effectively. Here are the steps typically followed in a structured risk assessment approach.
1. Define the Risk Assessment Methodology: Organizations must establish consistent procedures for risk assessment tailored to their context. The methodology outlines the criteria for assessing risks, such as how likelihood and impact are measured, and the organization's risk acceptance levels.
2. Identify Information Assets and Associated Risks: Starting with an asset inventory, potential risks are identified by linking assets to threats and vulnerabilities. This is often an iterative process incorporating input from various stakeholders and historical security data.
3. Analyze Risks (Likelihood and Impact): Each identified risk is evaluated for its probability of occurrence (likelihood) and the severity of consequences (impact) if it materializes. Organizations may use qualitative scales (e.g., high, medium, low) or quantitative measures (numerical scores) to rate risks. Both metrics help prioritize risks effectively.
4. Evaluate and Prioritize Risks: The combined assessment of likelihood and impact results in a risk level for each scenario, compared against pre-defined acceptance criteria. Risks exceeding the acceptable threshold are prioritized for treatment, while others may be monitored.
5. Document and Communicate Results: Risk assessment outcomes are documented in a risk register or report, specifying risk owners, evaluation details, and recommended mitigation actions. Transparency and communication help secure management commitment and guide control implementation.
6. Review and Update Regularly: Risk assessment is not a one-time activity but requires periodic review. Changes in organizational context, emerging threats, or control effectiveness necessitate updated evaluations to maintain ISMS relevance.
Risk Impact Evaluation
Impact assessment measures the magnitude of harm or loss that could occur if a risk event happens. Key impact areas include:
| Impact Area | Description |
| Financial Loss | Monetary damage resulting from fraud, theft, data loss, or regulatory penalties. |
| Operational Disruption | Downtime, reduced productivity, or halted business processes due to system or process failures. |
| Reputational Damage | Loss of trust and credibility among customers, stakeholders, or the public. |
| Legal and Regulatory Consequences | Fines, sanctions, or legal actions arising from violations of laws or regulations. |
| Privacy and Confidentiality Breaches | Unauthorized access, disclosure, or exposure of sensitive or personal information. |
Impact ratings typically align with organizational priorities to reflect what matters most strategically and operationally.
