Effective governance of an Information Security Management System (ISMS) is vital to ensure that information security policies and procedures are well organized, implemented, and maintained across an organization.
ISO/IEC 27001 emphasizes a clear definition and assignment of roles and responsibilities to create accountability and leadership commitment. This clarity supports the protection of information assets and ongoing compliance with security requirements.
Every individual’s duties related to information security must be understood and executed properly to foster a strong security culture.
Key Roles and Responsibilities
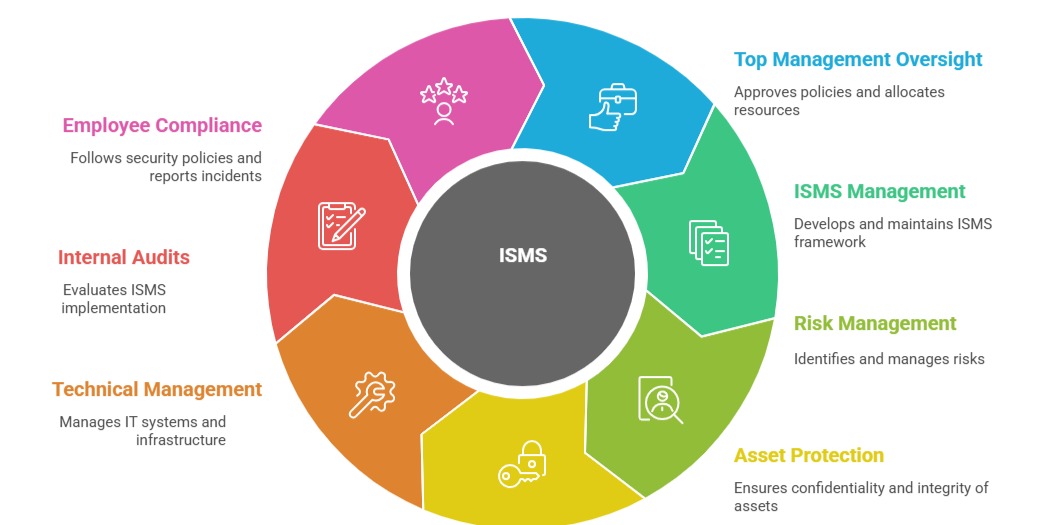
Each individual, from leadership to staff, plays an essential role in protecting organizational information. Here are the main responsibilities associated with key ISMS roles.
1. Top Management: Includes the CEO or equivalent, has ultimate accountability for the ISMS. Their responsibilities include approving the information security policy, allocating necessary resources, setting objectives, and regularly reviewing ISMS performance and compliance. They provide leadership, support, and direction that shape the security culture and priorities within the organization.
2. Information Security Manager (or Chief Information Security Officer - CISO): This role is critical for day-to-day management and coordination of the ISMS. The Information Security Manager develops and maintains the ISMS framework, oversees risk assessments and treatment plans, manages control implementations, and reports ISMS performance to senior management.
They ensure compliance with ISO 27001 requirements and drive continuous improvement efforts.
3. Risk Owners: They are individuals responsible for identifying, assessing, and managing risks within their designated areas. They must implement risk treatment plans and communicate risk status and any security concerns to the Information Security Manager or relevant stakeholders. Risk owners ensure localized accountability for addressing security risks efficiently.
4. Data Owners and Asset Owners: These roles involve the confidentiality, integrity, and availability of specific information assets. They approve access rights, ensure asset protection measures are followed, and support risk management activities associated with their assets.
5. System and Network Administrators: Responsible for the technical management, monitoring, maintenance, and security of IT systems and infrastructure to support the ISMS.
6. Internal Auditors: Their role is to independently evaluate ISMS implementation, identify nonconformities, and recommend corrective actions. Regular audits help maintain ISMS effectiveness and compliance.
7. All Employees: Every employee has a responsibility to comply with organizational security policies and procedures, report security incidents, and safeguard information they handle.
Purpose and Benefits of Clearly Defined Roles
Clearly defining and communicating roles and responsibilities accomplishes:
| Purpose / Benefit | Description |
| Improved Accountability | Clearly assigned roles ensure individuals understand and take responsibility for their security duties. |
| Enhanced Security Culture | Promotes awareness and commitment to information security across the organization. |
| Better Coordination | Strengthens alignment and collaboration in risk management and ISMS processes. |
| Smooth ISMS Operation | Supports the effective implementation, maintenance, and sustainability of the ISMS. |
| Easier Compliance Monitoring | Simplifies internal audits, performance tracking, and management reviews for continual compliance. |
These roles and responsibilities are usually documented in policies, job descriptions, and organizational charts. ISO/IEC 27001 clause 5.3 specifically requires that organizations allocate and communicate these roles effectively to ensure ISMS success.
