Selecting, implementing, and managing security controls is a central component of ISO/IEC 27001, ensuring that information security risks identified during risk assessments are effectively addressed.
Controls are safeguards or countermeasures aimed at protecting the confidentiality, integrity, and availability of information assets from threats and vulnerabilities.
The ISO 27001 standard, especially Annex A, offers a comprehensive catalog of controls that organizations can tailor to their risk environment and operational context.
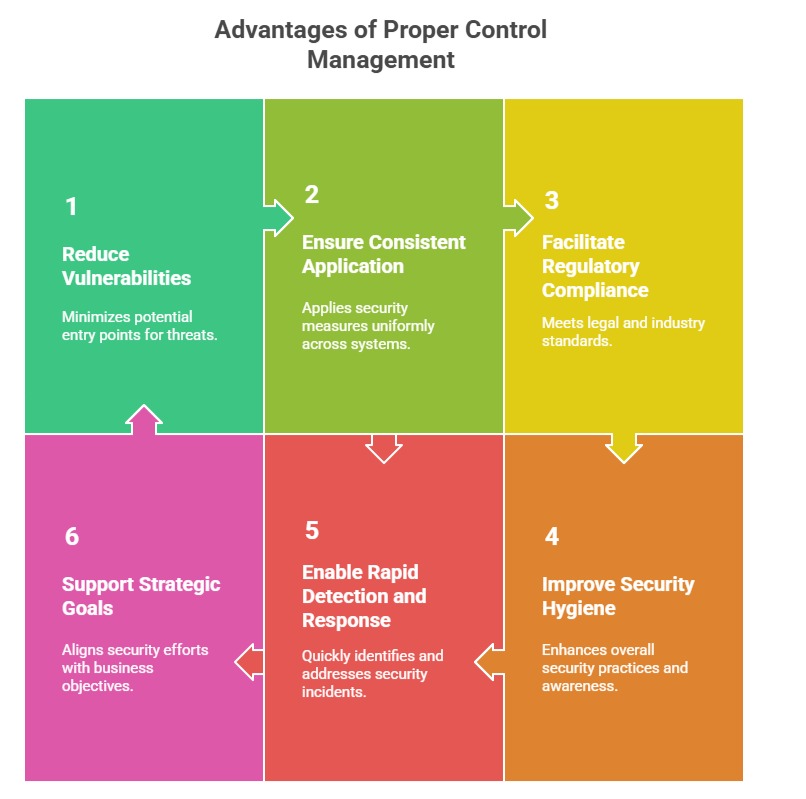
Proper control management strengthens the organization's security posture, ensures compliance, and supports continual improvement.
Selecting Security Controls
The selection process begins after risk assessments identify which risks require treatment. Organizations should:
1. Map identified risks to relevant Annex A controls, grouped across organizational, people, physical, and technological themes.
2. Consider the context, feasibility, cost, and effectiveness of each control.
3. Prioritize controls that mitigate the most critical risks while balancing operational impact.
4. Document decisions in the Statement of Applicability (SoA), which justifies the inclusion or exclusion of controls.
Implementing Security Controls
Effective implementation involves:
1. Developing clear procedures, guidelines, and policies that embed the controls within daily operations.
2. Assigning ownership and responsibilities for each control to ensure accountability.
3. Providing adequate training and awareness programs to equip personnel for their roles in control enforcement.
4. Leveraging technical solutions such as firewalls, encryption, access management tools, and monitoring solutions where applicable.
5. Ensuring physical measures like secure facilities, badges, and surveillance complement technological efforts.
Managing Security Controls
Ongoing management includes:
1. Monitoring control effectiveness through audits, reviews, and performance metrics.
2. Conducting regular internal audits and assessments to detect control failures or weaknesses.
3. Using incident reports and monitoring data to adapt and update controls.
4. Coordinating with management review processes to align controls with evolving business needs and threat landscapes.
5. Maintaining documentation to provide evidence for compliance audits and continual improvement efforts.
Class Sessions
Sales Campaign

We have a sales campaign on our promoted courses and products. You can purchase 1 products at a discounted price up to 15% discount.
