Identifying information assets, threats, and vulnerabilities is a foundational step in managing information security risks under ISO/IEC 27001.
Accurate identification ensures that organizations understand what valuable assets they possess, the risks those assets face, and the weaknesses that could be exploited.
This awareness enables targeted protection measures to safeguard confidentiality, integrity, and availability, fulfilling the ISMS objectives.
Identifying Information Assets
Information assets encompass more than just digital data; they include anything valuable to the organization that supports its business activities. This can include:
1. Electronic data and databases
2. Hardware (servers, computers, mobile devices)
3. Software applications and services
4. Intellectual property and proprietary information
5. Physical documents, records, and manuals
6. People (employees, contractors) who handle or have access to information
7. Facilities and infrastructure that support information processing
ISO 27001 requires organizations to create and maintain an asset inventory or register, listing all information assets within the ISMS scope. Each asset should have an assigned owner responsible for its security. Assets can be classified according to factors like sensitivity, criticality, and regulatory requirements.
Identifying Threats
A threat is any circumstance or event that has the potential to cause harm or loss to an information asset. Recognizing threats involves understanding potential attackers, accidental events, or environmental hazards. Common threat categories include:
| Threat Category | Examples |
| Cyber Threats | Malware, hacking, phishing, ransomware, and other malicious digital attacks target systems or data. |
| Human Threats | Insider threats, social engineering, or accidental human errors that compromise information security. |
| Physical Threats | Theft, natural disasters, fire, or equipment failure can damage or destroy assets. |
| Technical Failures | Software bugs, hardware malfunctions, or system crashes that disrupt operations. |
| External Events | Supply chain disruptions, regulatory changes, or geopolitical factors affecting information security. |
Organizations should identify relevant threats based on their context, historical incidents, and industry-specific risks.
Identifying Vulnerabilities
Vulnerabilities are weaknesses or gaps in an asset or its controls that can be exploited by threats to cause harm. Common vulnerabilities include:
1. Unpatched software or outdated systems
2. passwords or poor access controls
3. Lack of employee training or awareness
4. Inadequate physical security measures
5. Misconfigured networks or devices
6. Insufficient backup or recovery plans
Effective vulnerability identification often involves audits, penetration testing, security assessments, and monitoring.
Combining Asset, Threat, and Vulnerability Identification: Risk Assessment
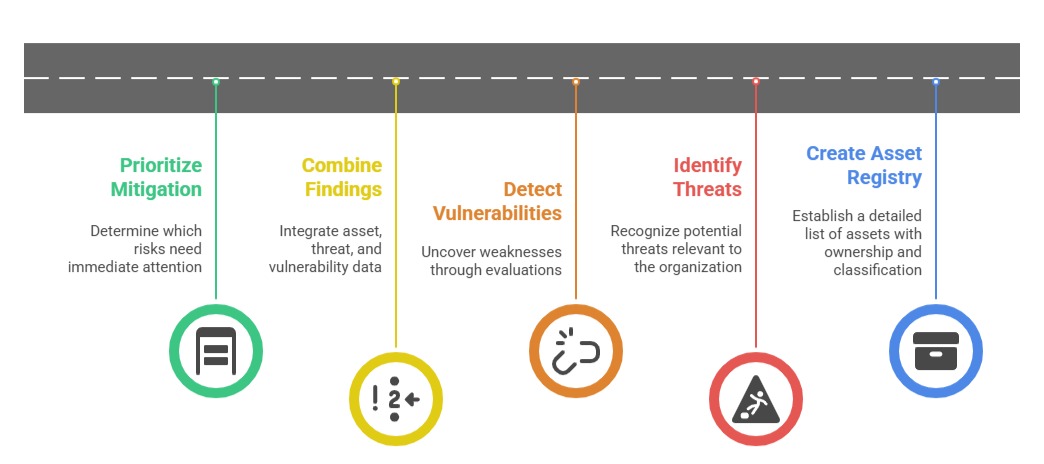
A thorough risk assessment integrates the identification of assets, threats, and vulnerabilities to evaluate the likelihood and impact of incidents. This process prioritizes which risks need treatment and informs decisions on security controls and resource allocation.
Steps
1. Create and maintain a comprehensive asset registry with ownership and classification.
2. Identify all plausible threats relevant to the organizational context.
3. Detect vulnerabilities through technical and procedural evaluations.
4. Combine findings in a risk assessment to prioritize mitigation efforts.
Class Sessions
Sales Campaign

We have a sales campaign on our promoted courses and products. You can purchase 1 products at a discounted price up to 15% discount.
