Internal audit processes and corrective actions are integral to maintaining and improving the effectiveness of an Information Security Management System (ISMS) as required by ISO/IEC 27001.
Internal audits provide a systematic, independent examination of the ISMS to verify conformity with the standard, organizational policies, and regulatory requirements.
They help identify gaps, weaknesses, and opportunities for improvement. Corrective actions ensure that identified nonconformities are addressed effectively to prevent recurrence and enhance the overall security posture.
Internal Audit Process

Internal audits help verify that the ISMS is functioning as intended and meeting standard requirements. Below are the essential stages of the internal audit process.
1. Audit Planning and Scope Definition: Establish an audit program that defines the frequency, scope, criteria, methods, responsibilities, and reporting procedures. The scope should cover relevant parts of the ISMS, focusing on critical processes and risk areas.
2. Auditor Selection: Auditors must be impartial and independent of the areas they audit to ensure objectivity. They should have the necessary competence and understanding of ISO 27001 requirements.
3. Evidence Collection and Document Review: Auditors review documented information such as policies, procedures, risk assessments, controls, and previous audit reports. They gather evidence through interviews, observations, and testing of security controls.
4. Conducting the Audit: Fieldwork involves assessing ISMS implementation and operation against criteria, verifying control effectiveness, and identifying nonconformities.
5. Audit Reporting: The audit report should detail findings, including nonconformities (major and minor), observations, and recommendations. It is communicated to relevant management and stakeholders for action.
6. Follow-up: Management reviews audit findings and initiates corrective action plans to address issues.
Corrective Actions
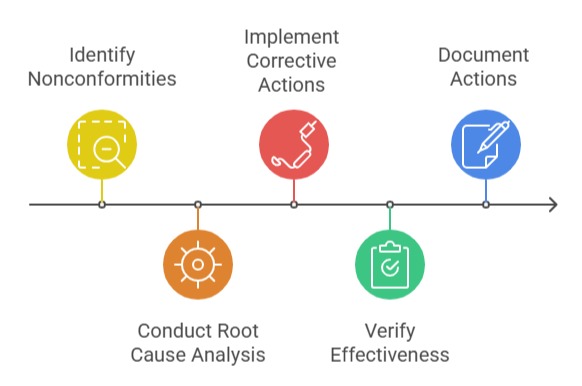
Implementing effective corrective actions strengthens the ISMS by resolving root causes of nonconformities. The following points outline the essential steps for handling them systematically.
1. Identification of Nonconformities: Nonconformities are deviations from ISO 27001 requirements or organizational policies identified during audits, monitoring, or incident investigations.
2. Root Cause Analysis: Understanding the underlying causes of nonconformities ensures that corrective actions address real issues rather than symptoms.
3. Implementation of Corrective Actions: Actions may include revising policies, enhancing controls, training, or process improvements. Responsibilities and timelines must be clearly defined.
4. Verification and Effectiveness Review: After implementation, the effectiveness of corrective actions is assessed to confirm that the issue is resolved and does not recur.
5. Documentation: All corrective actions, evidence of implementation, and reviews should be documented as part of the ISMS records.
Class Sessions
Sales Campaign

We have a sales campaign on our promoted courses and products. You can purchase 1 products at a discounted price up to 15% discount.
