DevSecOps is the natural and necessary evolution of DevOps, one that integrates security practices, tools, and responsibilities directly into every phase of the software development and delivery lifecycle, rather than bolting security on at the end.
The name itself communicates the intent: Development, Security, and Operations working together as one unified practice.
In a DevSecOps culture, security is not a separate team's problem, it is everyone's responsibility, built into every commit, every pipeline, and every deployment.
Why DevSecOps Emerged
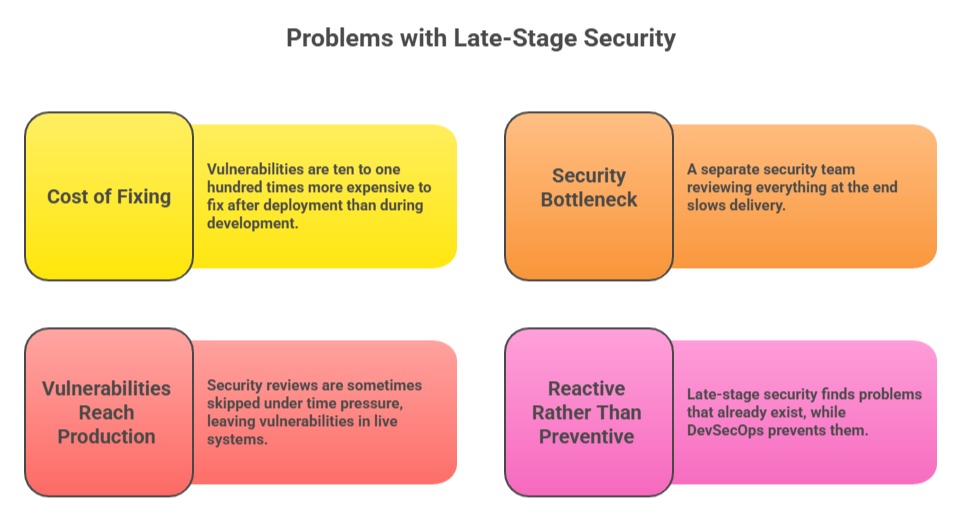
The traditional model of security in software development followed a simple but deeply flawed pattern, build the software first, then have a security team review it before release.
As DevOps accelerated delivery cycles from monthly releases to daily or hourly deployments, this approach became completely untenable.
What is DevSecOps?
DevSecOps is the practice of embedding security practices, automated security testing, and security-conscious culture into every phase of the DevOps lifecycle, from planning and coding through building, testing, deploying, and operating software in production.
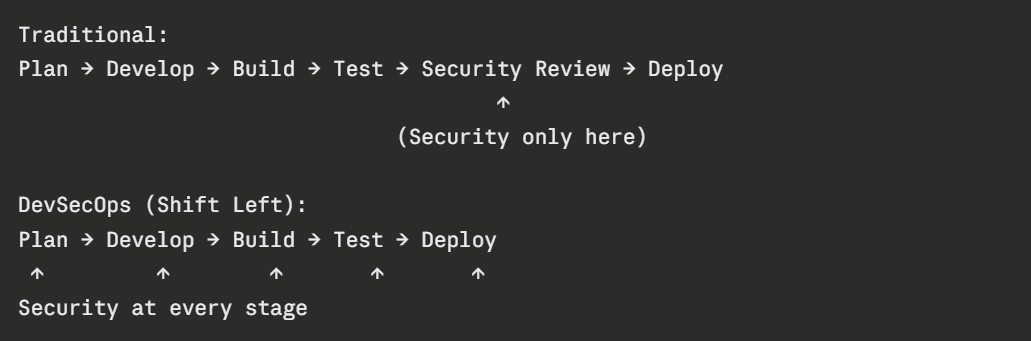
The guiding principle is often expressed as "shift left" — moving security earlier (to the left) in the delivery timeline, so that vulnerabilities are detected and addressed as close to the point of introduction as possible.
In DevSecOps:
1. Security requirements are defined during planning, not after the fact.
2. Developers write security-conscious code with access to real-time security feedback in their editors.
3. Automated security scans run in the CI/CD pipeline on every code change.
4. Infrastructure is provisioned with security controls defined as code.
5. Production systems are continuously monitored for security threats and anomalies.
6. The entire team, developers, operations engineers, and security professionals — shares responsibility for security outcomes.
The Shift Left Principle
Shifting left means:
1. Threat modeling during planning identifies risks before any code is written.
2. IDE plugins and pre-commit hooks catch security issues the moment a developer writes vulnerable code.
3. Automated scans in the CI pipeline reject insecure code before it is merged.
4. Security is a continuous, automated process — not a periodic manual review.
The earlier a vulnerability is found, the cheaper, faster, and less disruptive it is to fix.
Key DevSecOps Practices
1. Threat Modeling
During the planning phase, the team systematically identifies potential threats and attack vectors for the feature or system being built. This proactive analysis guides security decisions throughout development — before any code exists that needs to be fixed.
2. Secure Coding Standards
Developers follow established secure coding guidelines — input validation, proper error handling, avoiding hardcoded credentials, using parameterized queries to prevent SQL injection.
Security training ensures developers understand common vulnerabilities like those listed in the OWASP Top 10.
3. Pre-Commit Security Hooks
Git hooks can run security checks automatically before code is committed — scanning for hardcoded secrets, obvious vulnerabilities, or files that should not be committed. Tools like git-secrets and detect-secrets prevent sensitive credentials from ever reaching the repository.
4. Static Application Security Testing (SAST)
SAST tools analyze source code without running it to identify security vulnerabilities such as SQL injection, cross-site scripting (XSS), insecure cryptography, and buffer overflows. SAST runs automatically in the CI pipeline on every code push.
5. Software Composition Analysis (SCA)
Modern applications depend heavily on open-source libraries and third-party packages. SCA tools scan these dependencies for known vulnerabilities and outdated components.
Tools like Snyk and Dependabot alert teams when a dependency has a known security issue and suggest safe version upgrades.
6. Dynamic Application Security Testing (DAST)
Unlike SAST, DAST tests the running application by simulating attacks against it, probing for vulnerabilities that only appear at runtime, such as authentication bypasses, insecure API endpoints, and misconfigured security headers.
DAST runs against staging environments as part of the deployment pipeline.
7. Infrastructure Security as Code
Security controls for infrastructure — firewall rules, IAM policies, network configurations, encryption settings — are defined in IaC files (Terraform, CloudFormation) and enforced through automated policy checks.
Tools like Checkov and tfsec scan IaC files for security misconfigurations before infrastructure is provisioned.
8. Secrets Management
Credentials, API keys, and certificates are never hardcoded in code or configuration files.
They are stored in dedicated secrets management tools — HashiCorp Vault, AWS Secrets Manager, or Azure Key Vault, and injected into applications at runtime through secure, audited mechanisms.
9. Container Security
Container images are scanned for known vulnerabilities before being pushed to a registry. Tools like Trivy and Snyk Container identify vulnerable base images and packages. Images are built from minimal, trusted base images and run as non-root users.
10. Continuous Security Monitoring
Production systems are continuously monitored for security threats, unusual access patterns, privilege escalation attempts, unexpected network traffic, and known attack signatures.
Security Information and Event Management (SIEM) tools aggregate and analyze security events across the entire environment.
DevSecOps in the CI/CD Pipeline
Code Push
│
▼
Pre-commit hooks (secrets detection)
│
▼
SAST (static code analysis)
│
▼
SCA (dependency vulnerability scanning)
│
▼
Build and package
│
▼
Container image scanning
│
▼
IaC security scanning
│
▼
Deploy to staging
│
▼
DAST (dynamic application testing)
│
▼
Deploy to production
│
▼
Continuous security monitoring
Each stage acts as a security gate — code that fails a security check does not proceed further in the pipeline. This automated enforcement ensures security standards are applied consistently on every change, without relying on manual review.
Cultural Shift — Security as a Shared Responsibility
DevSecOps is as much a cultural shift as a technical one. The most important change it requires is moving security from being the exclusive domain of a dedicated security team to being a shared responsibility across the entire engineering organization.
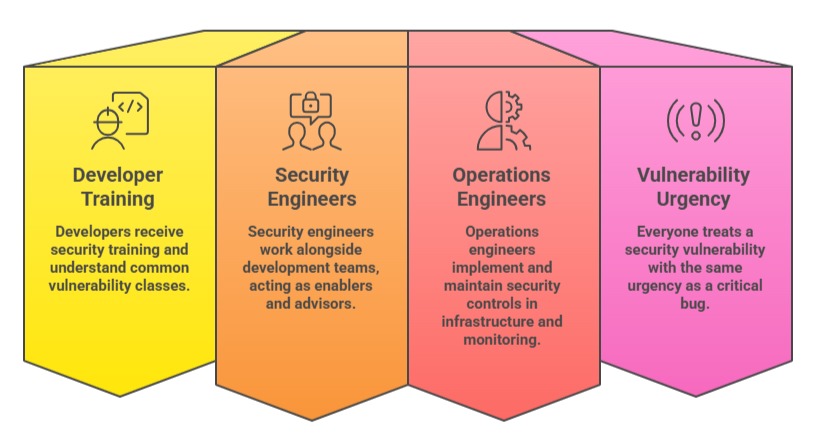
The security team's role evolves from reviewing and blocking releases to empowering teams with tools, training, and standards that allow them to ship securely at speed.