Security in cloud computing is a collaborative effort between the cloud service provider and the customer, which is clearly defined by the AWS Shared Responsibility Model.
This model helps businesses understand and manage the division of security duties, ensuring that both AWS and customers play crucial roles in maintaining a secure environment.
The model also grants businesses flexibility and control, allowing them to tailor security practices to their unique needs without deep technical complexity.
The AWS Shared Responsibility Model
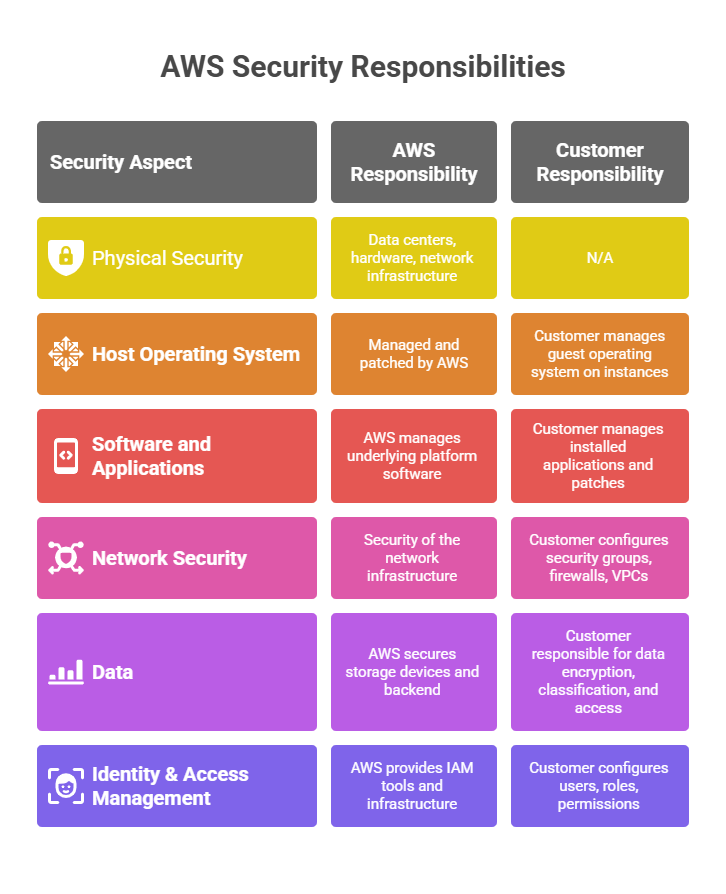
The shared responsibility model divides security tasks into two main categories:
1. Security of the Cloud (AWS’s responsibility): AWS is responsible for securing the infrastructure that supports the cloud services.This includes the physical data centres, hardware, software, networking, and facilities. Essentially, AWS handles the underlying foundation—maintaining and protecting the global infrastructure where services are run.
2. Security in the Cloud (Customer’s responsibility): Customers are responsible for securing whatever they deploy and manage within the cloud. This includes managing guest operating systems, software updates and patches, configuring firewalls and network security groups, managing access controls, encrypting data, and protecting applications.
The extent of customer responsibility varies based on the services used; for example, Infrastructure as a Service (IaaS) requires more customer control than abstracted services like storage.
Key Security Concepts
Below are the primary concepts that form the foundation of AWS’s security and governance model.
1. Data Protection: Customers retain control over their data security by encrypting data at rest and in transit using AWS tools and configuring proper access permissions.
2. Access Management: AWS provides Identity and Access Management (IAM) tools that customers use to regulate who can access AWS services and resources, ensuring only authorised users can perform actions.
3. Network Security: Customers configure network controls such as security groups and virtual private clouds (VPCs) to isolate and monitor traffic within their cloud environment.
4. Compliance and Certifications: AWS maintains compliance with global standards and provides documentation to help customers meet regulatory requirements, but customers must ensure their usage complies with applicable laws.
5. Shared Controls: In many cases, AWS manages physical and environmental controls, while customers handle application-level security controls, creating a shared security posture.
Importance of Understanding the Shared Responsibility Model
Knowing which security responsibilities AWS manages versus what customers must secure helps in designing robust security strategies.
Proper awareness ensures businesses do not overlook critical security areas or mistakenly assume AWS covers all security layers. This clarity reduces operational risks and aligns security efforts efficiently between AWS and the customer.
