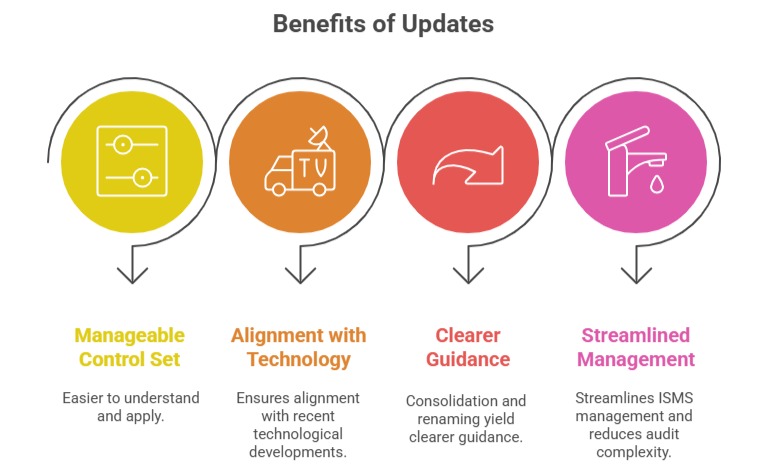
With the release of ISO/IEC 27001:2022, significant changes were made to Annex A controls to reflect the evolving landscape of information security. These changes include the identification of new controls, merging of existing ones, renaming for clarity, and removal of certain controls deemed redundant or outdated.
The adjustments aim to streamline the control framework, improve relevance to current technologies and threats, and facilitate easier implementation and auditing for organizations.
Identification of Changes in Controls
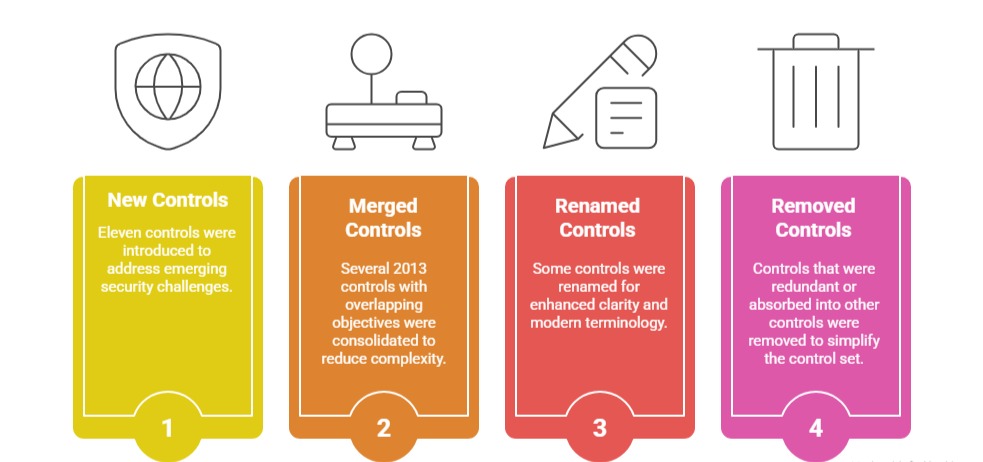
As part of the 2022 update, Annex A controls were revised to eliminate overlaps, modernize terminology, and introduce new categories. Here are the main changes reflected in the updated control structure.
1. New Controls: Eleven controls were introduced to address emerging security challenges, including but not limited to:
Threat Intelligence: To systematically gather and analyze information about potential cyber threats.
Information Security for Cloud Services: Addressing risks unique to cloud environments.
ICT Readiness for Business Continuity: Ensuring information and communication technology supports ongoing operations during disruptions.
Physical Security Monitoring: Enhancing proactive detection of physical security incidents.
Configuration Management: Controlling system setups to prevent unauthorized changes.
Information Deletion: Secure removal of information to prevent unauthorized access.
Data Masking and Leakage Prevention: Protecting sensitive data from unauthorized disclosure.
Monitoring Activities, Web Filtering, and Secure Coding: Addressing operational and software security aspects in depth.
2. Merged Controls: Several 2013 controls with overlapping objectives were consolidated to reduce complexity. For example:
Access Control mechanisms representing various facets were merged into comprehensive controls covering logical access and user management.
Multiple asset management-related controls were combined under unified categories.
Controls related to system acquisition, development, and maintenance were merged to facilitate streamlined software and hardware security management.
3. Renamed Controls: Some controls were renamed for enhanced clarity and modern terminology. For instance:
“Information Transfer Policies” became “Information Transfer” to encompass broader communication methods.
“Cryptographic Controls” was refined to “Cryptographic Protection” to indicate a focus on safeguarding information.
Names were adjusted to better reflect control purposes in a contemporary cybersecurity context.
4. Removed Controls: Controls that were redundant or absorbed into other controls were removed to simplify the control set without losing security coverage. For example:
“Mobile Computing and Teleworking” controls were integrated into other relevant controls addressing remote work security.