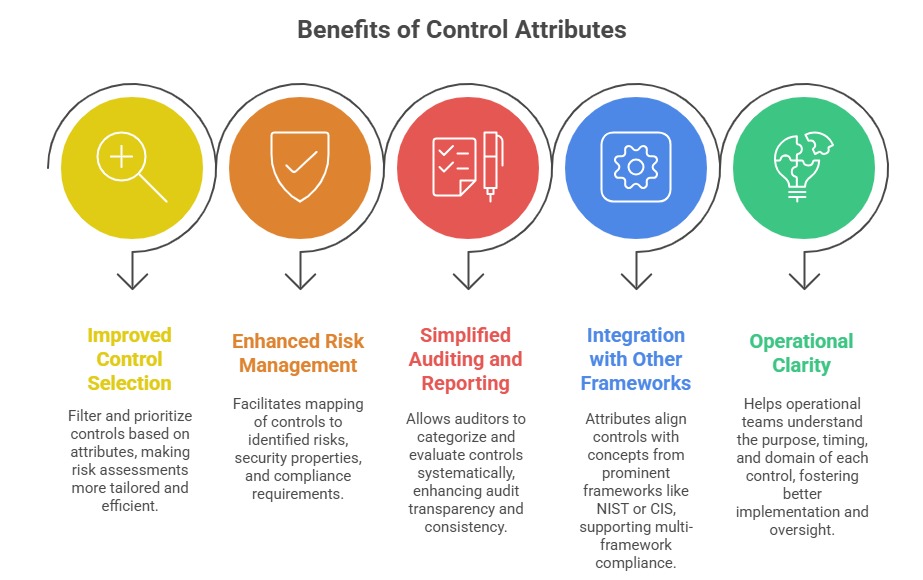
One of the noteworthy additions in the ISO/IEC 27001:2022 revision is the introduction of attributes to Annex A controls. These attributes serve as a new taxonomy to classify, describe, and better manage the controls within the Information Security Management System (ISMS).
By assigning attributes, the standard provides a more structured way to understand, select, and implement controls based on specific characteristics and organizational needs. This enhancement greatly aids organizations in aligning their security controls with risk profiles, operational contexts, and industry best practices.
What are Control Attributes
Control attributes are metadata assigned to each control in Annex A, encompassing various perspectives such as the control type, security goals addressed, cybersecurity functions, operational capabilities, and security domains. These attributes serve as a multidimensional framework to facilitate better analysis and implementation of controls.
Types of Control Attributes
The 2022 version of ISO/IEC 27001 introduces control attributes to help organizations better categorize, analyze, and apply controls. Here are the main types of attributes used to classify each control.
1. Control Type: Categorizes controls based on their function in managing risk over time.
Preventive: Designed to prevent security incidents from occurring.
Detective: Activate or alert when a security incident is happening.
Corrective: Act after an incident to mitigate damage and restore normalcy.
2. Information Security Properties: Identifies the core information security principles that the control supports.
Confidentiality (preventing unauthorized access),
Integrity (ensuring data accuracy and completeness), and
Availability (ensuring data and services are accessible when needed).
3. Cybersecurity Concepts: Aligns controls with cybersecurity lifecycle functions following ISO/IEC TS 27110.
Identify, Protect, Detect, Respond, and Recover.
4. Operational Capabilities: Maps controls to practical security domains relevant to organizational operations, such as governance, asset management, system security, human resources security, threat and vulnerability management, and legal compliance.
5. Security Domains: Assigns controls into four broad domains to unify organizational security efforts.
Governance and Ecosystem,
Protection,
Defence,
Resilience.