Containment strategies are critical actions taken during the incident response process to limit the scope and impact of a security incident.
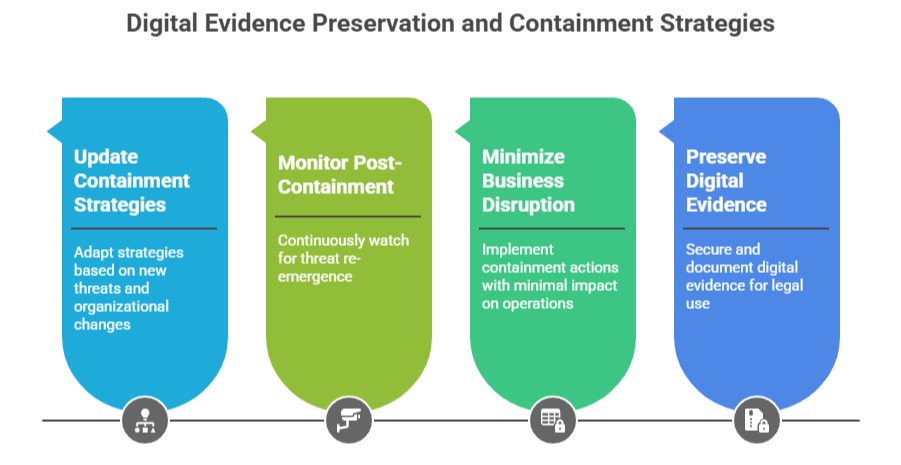
The primary goal of containment is to prevent the incident from spreading, minimize damage, preserve evidence for investigation, and maintain operational continuity as much as possible.
Proper containment is a balance between swift action and careful planning, as aggressive containment may disrupt essential business functions or compromise forensic data.
ISO/IEC 27035 highlights the importance of tailored containment measures that fit the unique context and risks of each incident.
Short-Term Containment
Short-term containment focuses on immediate tactics to halt the spread of the incident and mitigate urgent risks. Examples include:
1. Isolating affected systems by disconnecting them from the network or disabling compromised accounts to prevent lateral movement and further exploitation.
2. Blocking malicious IP addresses or network ports using firewalls or intrusion prevention systems (IPS).
3. Applying temporary security controls, such as network segmentation or access restrictions, to contain affected zones.
The objective is to implement these measures quickly to stabilize the situation and buy time for a more thorough response.
Long-Term Containment
Long-term containment involves more comprehensive and sustainable actions that allow business operations to continue while preventing recurrence of the incident. Measures may include:
1. Deploying permanent firewall rules and security patches to address vulnerabilities exploited in the attack.
2. Reconfiguring user permissions and access controls to align with the principle of least privilege.
3. Strengthening monitoring systems with enhanced detection rules based on indicators of compromise identified during the incident.
4. Conducting employee training targeted at behaviors that contributed to the incident.
Long-term containment requires coordination between security, IT, and business teams to balance security improvements with operational needs.
Class Sessions
Sales Campaign

We have a sales campaign on our promoted courses and products. You can purchase 1 products at a discounted price up to 15% discount.
