Monitoring and alerting systems are a cornerstone of any robust information security framework.
They enable organizations to maintain continuous oversight of their IT environment by tracking activities, detecting anomalous behaviors, and sending timely alerts to respond to emerging threats.
Properly implemented, these systems not only reduce the risk of undetected security incidents but also empower faster remediation, minimizing business impact.
ISO/IEC 27035 and related standards highlight monitoring and alerting as essential for proactive security management and incident response.
Core Functions and Best Practices
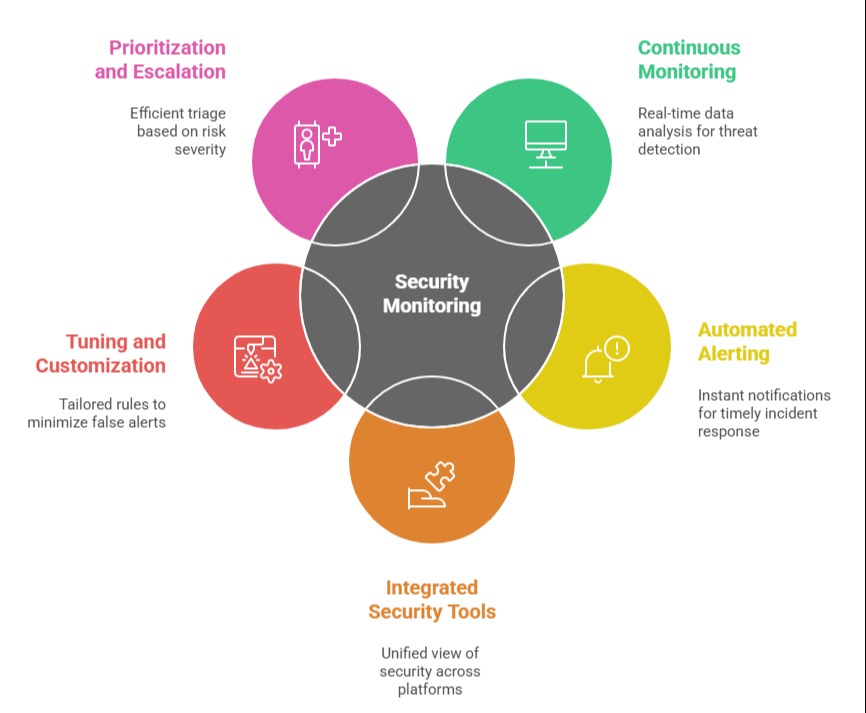
Here are the essential functions and best practices that form the foundation of a strong monitoring and alerting framework for effective incident response.
1. Continuous Monitoring
Monitoring tools regularly collect and analyze system, network, and application data to detect threats or operational anomalies.
These systems provide the foundation for identifying suspicious activities in real time or near-real time by observing patterns, outliers, or policy violations across endpoints, servers, cloud platforms, and network devices.
2. Automated Alerting
When monitoring identifies a condition that deviates from normal baselines or matches known threat indicators, the system generates alerts.
These notifications inform responsible personnel (such as SOC analysts or IT administrators) through dashboards, emails, messages, or integrations with incident management platforms.
Automated alerting helps prioritize incidents, ensuring prompt attention to the most urgent risks.
3. Integrated Security Tools
Modern monitoring and alerting systems frequently combine data from Security Information and Event Management (SIEM), Intrusion Detection/Prevention Systems (IDS/IPS), Endpoint Detection and Response (EDR), and other platforms.
Integration ensures a unified, comprehensive view of security across the organization.
4. Tuning and Customization
Systems should be regularly tuned to minimize false positives and false negatives, targeting relevant threats while avoiding alert fatigue.
Custom rules, baselines, and escalation workflows tailored to an organization’s environment improve detection and response effectiveness.
5. Prioritization and Escalation
Advanced monitoring systems can categorize alerts by severity and impact, enabling efficient triage and escalation based on organizational risk criteria. This ensures critical incidents are addressed without delay.
Class Sessions
Sales Campaign

We have a sales campaign on our promoted courses and products. You can purchase 1 products at a discounted price up to 15% discount.
