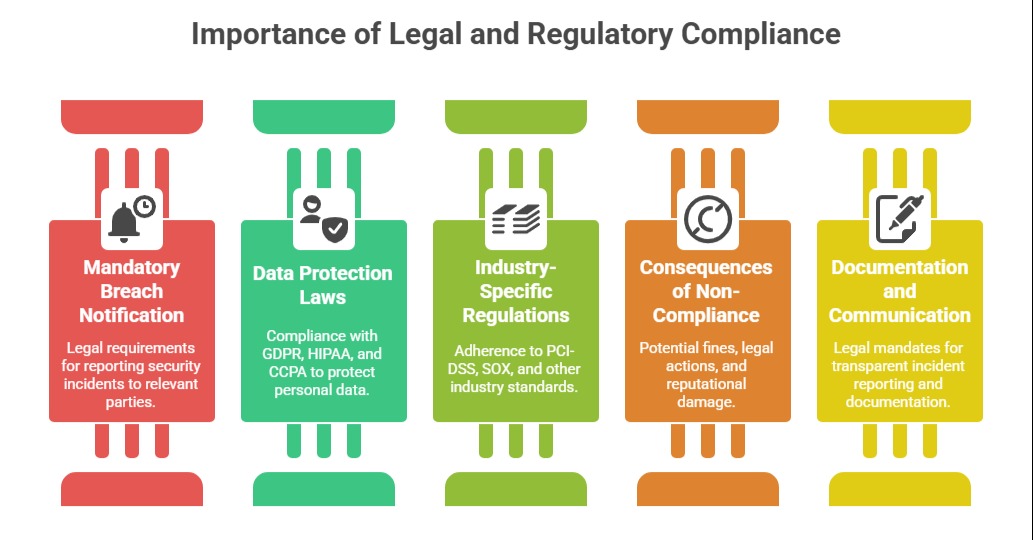
Legal and regulatory considerations are critical components of effective information security incident management.
Organizations must navigate a complex landscape of laws, regulations, and contractual obligations that govern how security incidents are detected, reported, and managed.
Compliance with these legal requirements not only helps avoid penalties and reputational damage but also supports transparency, accountability, and trust among stakeholders.
ISO/IEC 27035 recognizes these considerations as integral, encouraging organizations to incorporate them into their incident management processes from preparation through resolution.
Integrating Legal and Regulatory Requirements
Organizations should maintain an up-to-date understanding of applicable laws and regulations and reflect these in their incident management policies and response plans. This includes:
1. Defining criteria for incident classification that trigger mandatory notifications;
2. Establishing protocols for timely internal and external communications, including legal counsel involvement;
3. Ensuring preservation of evidence to support forensic investigations and potential legal actions;
4. Training incident response teams on relevant legal responsibilities and privacy considerations.
Incident Documentation and Reporting
ISO/IEC 27035 stresses comprehensive and consistent incident documentation to enable clear evidence trails and support regulatory reporting. Documentation should capture detection timelines, actions taken, communication logs, and lessons learned.
Organizations may also need to prepare formal reports for regulators or data protection authorities that detail the incident impact, response effectiveness, and mitigation measures.
Coordination with External Entities
In many cases, organizations must coordinate incident management efforts with external parties such as law enforcement, regulators, affected customers, third-party service providers, or cybersecurity authorities.
Clear communication channels and pre-established escalation procedures help manage these interactions smoothly and compliantly.
Class Sessions
Sales Campaign

We have a sales campaign on our promoted courses and products. You can purchase 1 products at a discounted price up to 15% discount.
