Incident impact assessment is a crucial phase in the information security incident management process that determines the extent and severity of harm caused by a security incident to an organization’s assets, operations, and stakeholders.
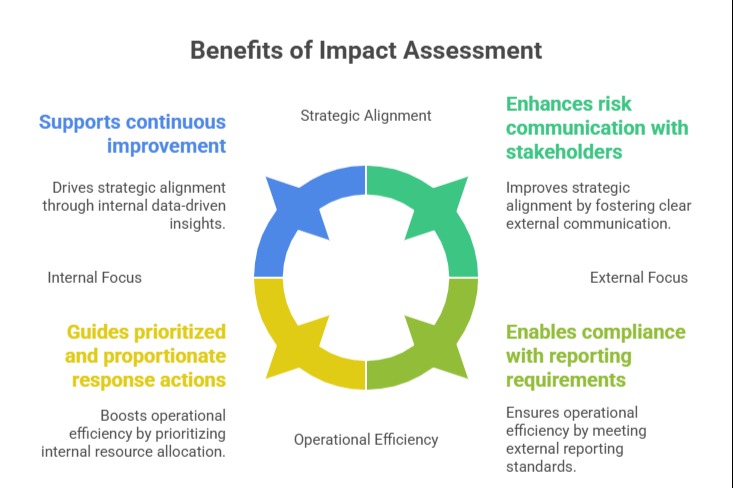
This assessment guides the prioritization of response efforts and resource allocation to minimize damage and ensure effective mitigation.
ISO/IEC 27035 emphasizes the importance of a thorough, structured impact assessment to support informed decision-making and to tailor response actions based on identified risks and potential consequences.
Key Aspects of Incident Impact Assessment
Incident impact assessment provides a structured approach to understanding how an event affects operations, assets, and stakeholders. The following aspects outline critical considerations for accurately measuring and prioritizing incident response.
1. Scope of Impact: Assess which parts of the organization are affected, including information systems, business processes, personnel, and external parties such as customers and partners. Understanding the scope helps prevent underestimating or overlooking critical areas of impact.
2. Types of Impact: Impact can be multidimensional, including:
| Type of Impact | Description |
| Confidentiality | Unauthorized disclosure of sensitive or confidential information. |
| Integrity | Unauthorized modification, alteration, or destruction of data compromises its accuracy and reliability. |
| Availability | Disruption or denial of access to information systems, services, or resources required for operations. |
| Financial | Direct and indirect financial losses, including remediation costs, regulatory fines, and loss of revenue. |
| Reputation | Damage to organizational credibility, brand image, or stakeholder confidence. |
| Compliance | Violations of legal, regulatory, or contractual obligations resulting in penalties or sanctions. |
3. Severity Levels: Assigning severity levels (e.g., low, medium, high, critical) based on impact magnitude supports prioritization. These levels are defined with quantitative and qualitative criteria suited to organizational risk tolerance and business context.
4. Time Sensitivity: Identify time-critical processes and the urgency for incident resolution to mitigate prolonged impact. Some impacts may be immediate and severe, requiring rapid containment, while others may have delayed effects.
5. Stakeholder Considerations: Evaluate the potential effects on internal and external stakeholders, ensuring their needs and concerns influence response strategies and communication plans.
Class Sessions
Sales Campaign

We have a sales campaign on our promoted courses and products. You can purchase 1 products at a discounted price up to 15% discount.
