In the realm of incident management, establishing clear escalation procedures and communication plans is critical for ensuring a swift, coordinated, and effective response to security incidents.
Proper escalation protocols prevent delays in addressing serious incidents, help prioritize response efforts, and ensure that relevant stakeholders and authorities are informed promptly.
As emphasized by ISO/IEC 27035, a structured escalation and communication plan supports transparency, accountability, and resilience, especially in complex or high-impact security situations.
Elements of Incident Escalation and Communication Plans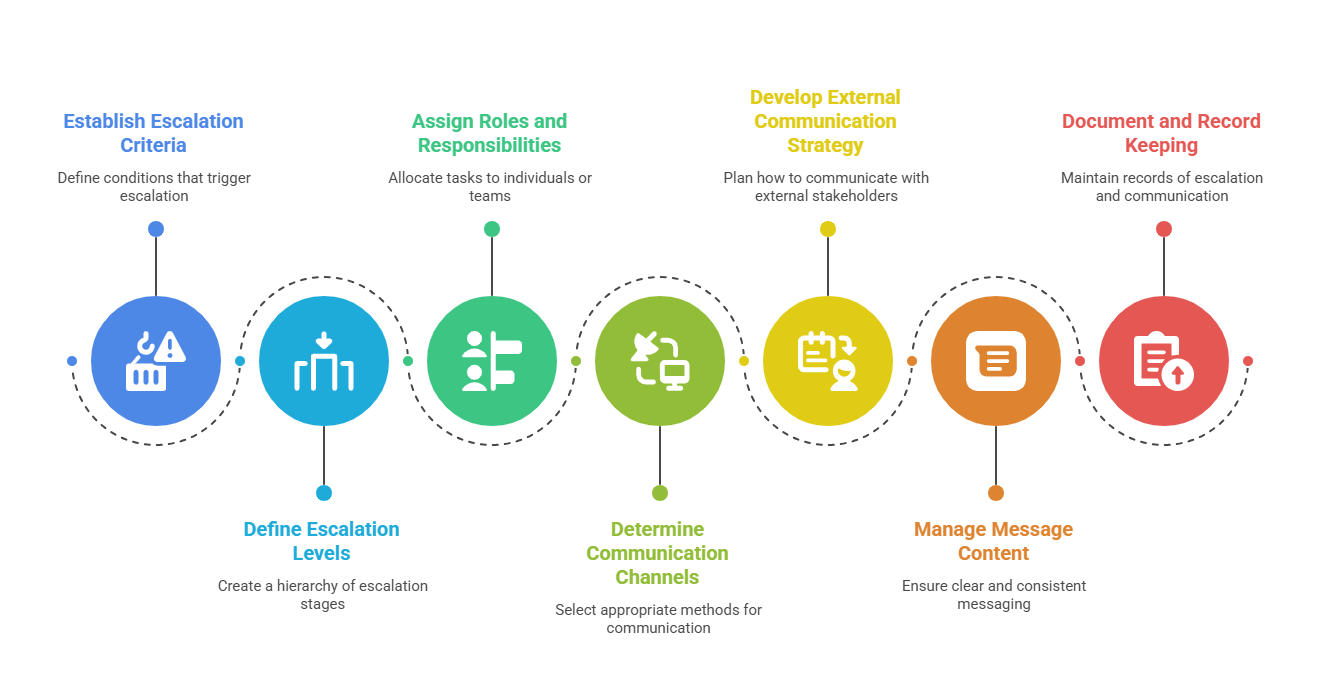
Here are the key elements organizations should include in their escalation and communication plans to ensure timely decisions, accurate messaging, and coordinated action.
1. Criteria for Escalation
Establish specific, measurable criteria that trigger escalation to higher authority levels. These could include incident severity, potential impact on business operations, data sensitivity, or breach size.
Clear criteria prevent unnecessary escalations and ensure the timely handling of critical incidents.
2. Defined Escalation Levels
Develop escalation paths for different incident types and severity levels. For example, minor incidents might be managed by operational teams, while major incidents require executive oversight or external notification.
Structuring escalation levels facilitates consistency and reduces response ambiguity.
3. Roles and Responsibilities
Clarify who is responsible for initiating escalation, communication, and decision-making at each level. Assign specific roles such as Incident Manager, Communications Lead, Legal Advisor, and Senior Management, ensuring accountability and prompt action.
4. Communication Channels and Timing
Identify formal channels for internal and external communication, including email, messaging platforms, hotlines, or incident management systems.
Define the timing of updates—initial alerts, ongoing status reports, and post-incident summaries—to maintain stakeholder trust and reduce confusion.
5. External Communication Strategy
Develop protocols for engaging external parties such as regulatory authorities, law enforcement, customers, or vendors.
External communication should be coordinated, factual, and compliant with legal and regulatory requirements, especially concerning breach notifications and public relations.
6. Message Management
Create templates and guidelines to ensure consistent, accurate, and clear messaging. Establish procedures for verifying facts before dissemination to avoid misinformation.
7. Documentation and Record Keeping
Maintain detailed records of escalation triggers, decisions, and communications. Proper documentation supports compliance audits and post-incident analysis.
Class Sessions
Sales Campaign

We have a sales campaign on our promoted courses and products. You can purchase 1 products at a discounted price up to 15% discount.
